Connected transportation systems depend heavily on trust. Every message exchanged between vehicles and infrastructure must be authentic, timely, secure, and verifiable.
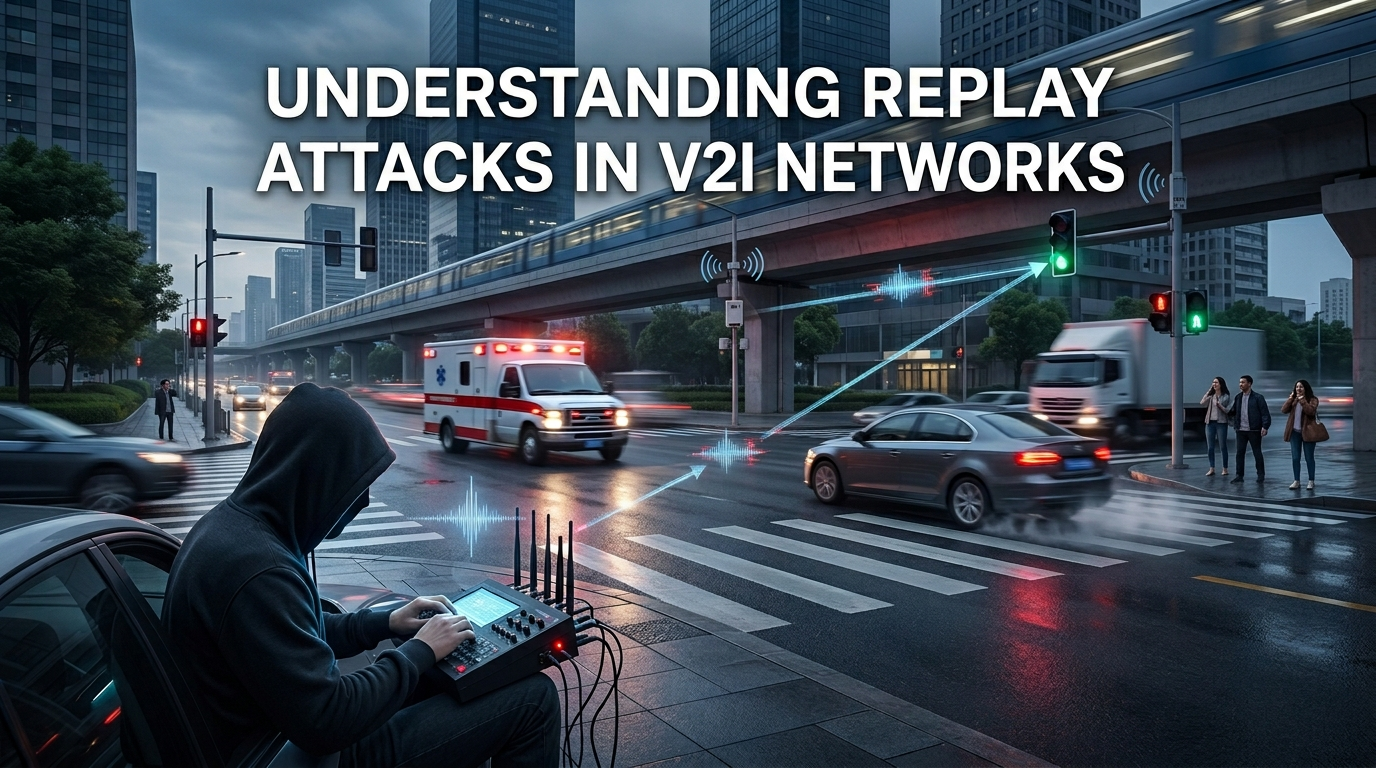
Without proper safeguards, attackers can exploit communication systems through one of the most dangerous threats in wireless infrastructure: replay attacks.
What Is a Replay Attack?
A replay attack occurs when a malicious actor captures a legitimate communication packet and retransmits it later to trigger unauthorized behavior. In intelligent traffic systems, this could potentially activate false green signals, disrupt traffic coordination, manipulate emergency routing, create intersection conflicts, and compromise public safety.
According to IBM Cybersecurity Learning Center, replay attacks are common in systems where message freshness is not properly validated.
Our Protection Mechanisms
At Greenwave TechLabs, replay attack prevention became a critical design requirement within our secure LoRa V2I architecture. Our communication framework uses timestamp verification, HMAC authentication, secure packet validation, and replay rejection logic to ensure communication integrity.
The Validation Workflow
- Emergency vehicle transmits an authenticated LoRa packet
- Packet includes a timestamp and verification token
- Traffic intersection validates authenticity
- Timestamp freshness is checked
- Expired or duplicated packets are rejected
Our implementation used a narrow timestamp acceptance window of approximately ±2 seconds, significantly reducing replay vulnerability.
Multi-Modal Defense
According to OWASP Replay Attack Overview, modern secure communication systems must combine cryptographic authentication, timestamp validation, nonce verification, and session integrity checks to prevent replay exploitation.
In our architecture, security does not depend on communication alone. The system also cross-validates acoustic siren detection, visual confirmation, and authenticated V2I packets through multi-modal fusion logic. This layered design makes spoofing and replay attacks significantly harder to execute successfully.
As transportation systems evolve into intelligent connected networks, cyber resilience will become as important as mobility itself. Because in future smart cities, every traffic signal becomes part of a cybersecurity surface.